All Categories
Featured
Table of Contents
In 2020, the class will certainly be used both in the Summer term and in the Autumn term. The Summer offering will be more targeted in the direction of trainees with software program design experience (e.g., software application engineering training course, commercial experience, or internship experience), but will certainly anticipate no information science history. The Autumn offering will be targeted extra at pupils with some data scientific research experience (e.g., a maker learning training course on campus or online), however will anticipate no software application design history.
See below for details modifications. For researchers, teachers, or others interested in this subject, we share all course material under an imaginative commons license on GitHub () and have actually just recently released a post describing the rationale and the style of this course: Mentor Software Design for AI-Enabled Solutions. We would certainly enjoy to see this training course or a similar version showed someplace else.
It will certainly concentrate mainly on sensible techniques that can be made use of currently and will include hands-on experiment modern tools and infrastructure. 17-445/17 -645, 12 Devices Open to undergraduate and graduate pupils meeting the prerequisites. The summer season 2020 offering targets students with a software program engineering background (see requirements below) Lectures: Tuesday+Thursday 3-4:20 pm, online via zoom Recitation: Wednesday 12:30 -1:50 pm, online by means of zoom Teacher: Christian Kaestner TA: Shreyans Sheth Workplace Hours: after each lecture We use Canvas for statements and discussions.
I will constantly stick about after class to respond to concerns and enjoy to transfer to a personal channel if you request so. The training course web content evolves from term to term. See the program material of the Fall 2019 term to obtain an introduction and look at our Understanding Goals.
, Ch.
21 & Product: Organizing Google's Datasets Tue, Jul 28 Safety, Adversarial Understanding, and Privacy (md, pdf, video, train) Structure Intelligent Equipments, Ch. 13 & Prediction devices, Ch. 19 Joined, Jul 29 Thu, Jul 30 Security (md, pdf, video) Tue, Aug 04 Fostering Interdisciplinary Teams (md, pdf, video) Thu, Aug 06 Recap and Evaluation (md, pdf, video clip) Fri, Aug 07 The program uses Canvas for uploading slides, analyses, and videos, for discussions, for tests, news, and supplemental files; Gradescope (connected from Canvas) is used for research entries and grading; GitHub is made use of to coordinate group work.
The 10-Second Trick For Top Machine Learning Courses Online
We will have an open-book midterm during a lecture timeslot and project/homework presentations over Zoom. We assure to never ever use any type of proctoring or attention-checking devices. Live involvement and activated electronic cameras exist to create a much better and more inclusive learning experience, not to spy on you or force you to listen.
Note that we do rule out mere passive visibility as engagement, however just energetic engagement. While mentor remotely, we'll provide a 10% incentive on the involvement quality for keeping a video camera transformed on throughout class. We will certainly offer comments at mid-semester so you can check in on just how you're doing.

Teamwork is a vital part of this training course. Several projects and a final job are done in groups of 3-5 students. Groups will be assigned by the teacher and stay with each other for multiple tasks and a last task. A team plan posted on Canvas uses and defines roles and groups and how to handle conflicts and discrepancies.
We make news with Canvas and usage Canvas also for conversations, consisting of clarifying research assignments and other communications. We will certainly be using Goeff Hulten's "Building Intelligent Systems: A Guide to Device Learning Design" (ISBN: 1484234316) throughout much of the course.
The Only Guide to How I Went From Software Development To Machine ...

In enhancement, we will certainly supply added supplementary analyses, consisting of article and scholastic papers, throughout the semester. Evaluation will certainly be based on the following distribution: 35% individual projects, 20% midterm, 30% team job, 10% involvement, 5% analysis quizzes. This is a 12-unit course, and it is our intention to handle it to ensure that you spend near 12 hours a week on the training course, on standard.
Notification that some homework is performed in groups, so please make up the overhead and decreased time adaptability that comes with groupwork. Please really feel totally free to offer the training course team feedback on how much time the training course is taking for you. Late operate in private jobs will be accepted with a 10% fine daily, for approximately 3 days.
Lots of research assignments have an element that requires reviewing issues in written form or mirroring concerning experiences. To practice creating abilities, the Global Communications Facility (GCC) offers one-on-one help for pupils, along with workshops.
We anticipate that team members work together with one another, but that groups work individually from one another, not exchanging results with various other groups. Within groups, we expect that you are sincere about your contribution to the group's work.
What Does Software Engineering Vs Machine Learning (Updated For ... Mean?
You may not look at another trainee's option, even if you have completed your own, neither may you knowingly provide your solution to an additional pupil or leave your remedy where another pupil can see it. Below are some examples of actions that are inappropriate: Duplicating or retyping, or referring to, data or parts of documents (such as resource code, written message, or device examinations) from an additional person or source (whether in final or draft form, no matter of the consents set on the linked data) while producing your own.
Writing, utilizing, or sending a program that tries to modify or remove grading details or otherwise concession safety of program sources. Lying to training course staff.
Be cautious the privacy settings on your open source accounts! Coaching others step-by-step without them comprehending your assistance. If any one of your work consists of any statement that was not written by you, you must put it in quotes and point out the source. If you are paraphrasing a concept you read somewhere else, you must recognize the resource.
If there is any type of inquiry regarding whether the material is allowed, you should obtain approval ahead of time. We will be utilizing automated systems to find software plagiarism. It is ruled out disloyalty to clear up unclear points in the assignments, talks, lecture notes; to offer aid or get aid in using the computer system systems, compilers, debuggers, profilers, or other centers; or to review concepts at an extremely high degree, without describing or producing code.
The minimal charge for dishonesty (including plagiarism) will certainly be a no grade for the entire task. Ripping off events will certainly also be reported with College networks, with feasible added disciplinary action (see the above-linked University Plan on Academic Integrity).
We will certainly deal with you to guarantee that lodgings are provided as ideal. If you presume that you might have a special needs and would take advantage of lodgings however are not yet signed up with the Office of Special Needs Resources, we urge you to call them at [email protected]!.?.!. Please look after yourself.
6 Simple Techniques For Certificate In Machine Learning
Requesting support quicker instead of later on is commonly valuable. If you or anybody you know experiences any kind of scholastic tension, tough life occasions, or sensations like stress and anxiety or clinical depression, we strongly urge you to look for assistance. Therapy and Mental Services (CaPS) is right here to help: call 412-268-2922 and see their web site at http://www.cmu.edu/counseling/.
You probably understand Santiago from his Twitter. On Twitter, every day, he shares a great deal of useful points concerning maker understanding. Alexey: Prior to we go into our major topic of moving from software program engineering to maker understanding, maybe we can start with your history.
I went to university, got a computer system science level, and I started developing software application. Back after that, I had no idea about device discovering.
6 Simple Techniques For Aws Certified Machine Learning Engineer – Associate
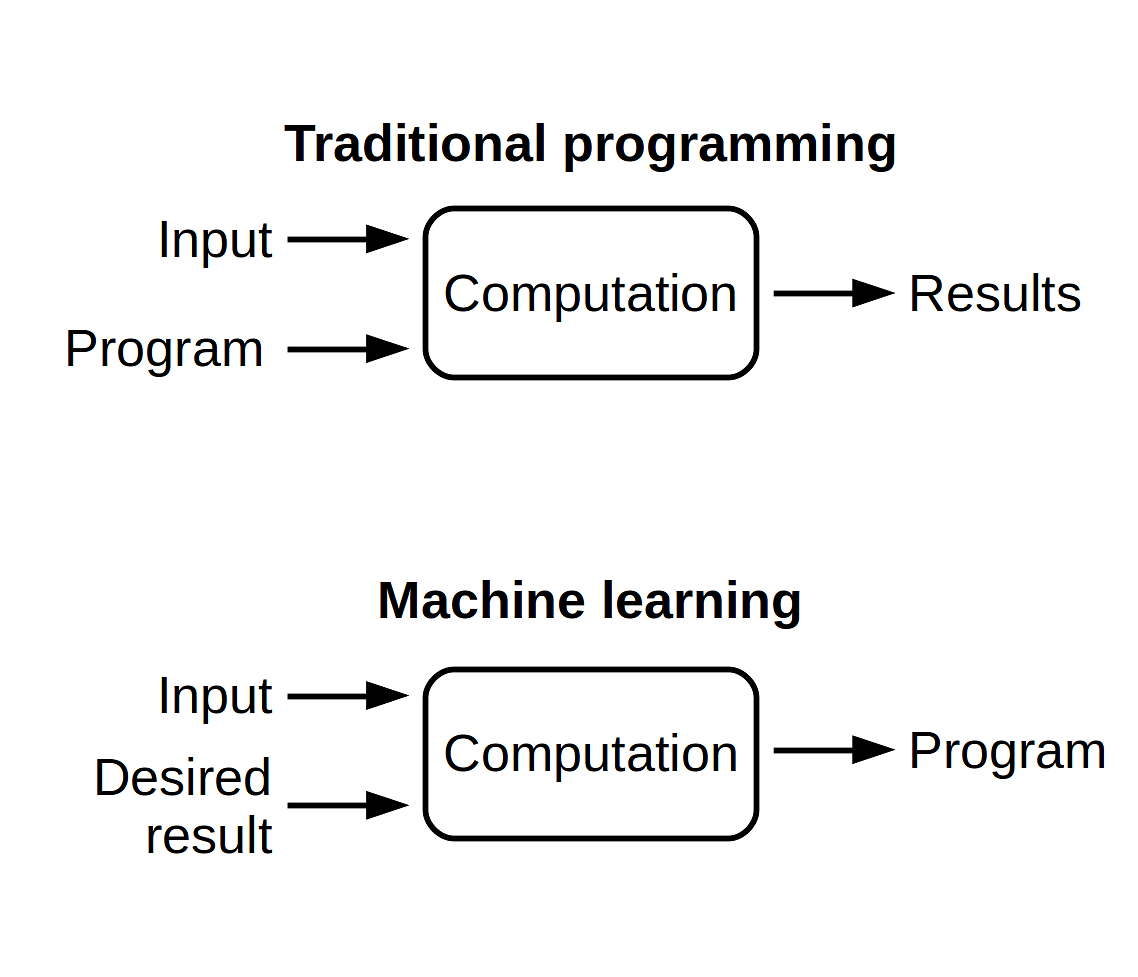
I understand you have actually been using the term "transitioning from software application engineering to artificial intelligence". I such as the term "including to my capability the artificial intelligence abilities" extra due to the fact that I believe if you're a software program designer, you are currently supplying a great deal of value. By including artificial intelligence now, you're enhancing the effect that you can carry the sector.
Table of Contents
Latest Posts
How To Answer Algorithm Questions In Software Engineering Interviews
22 Senior Software Engineer Interview Questions (And How To Answer Them)
The Easy Way To Prepare For Software Engineering Interviews – A Beginner’s Guide
More
Latest Posts
How To Answer Algorithm Questions In Software Engineering Interviews
22 Senior Software Engineer Interview Questions (And How To Answer Them)
The Easy Way To Prepare For Software Engineering Interviews – A Beginner’s Guide